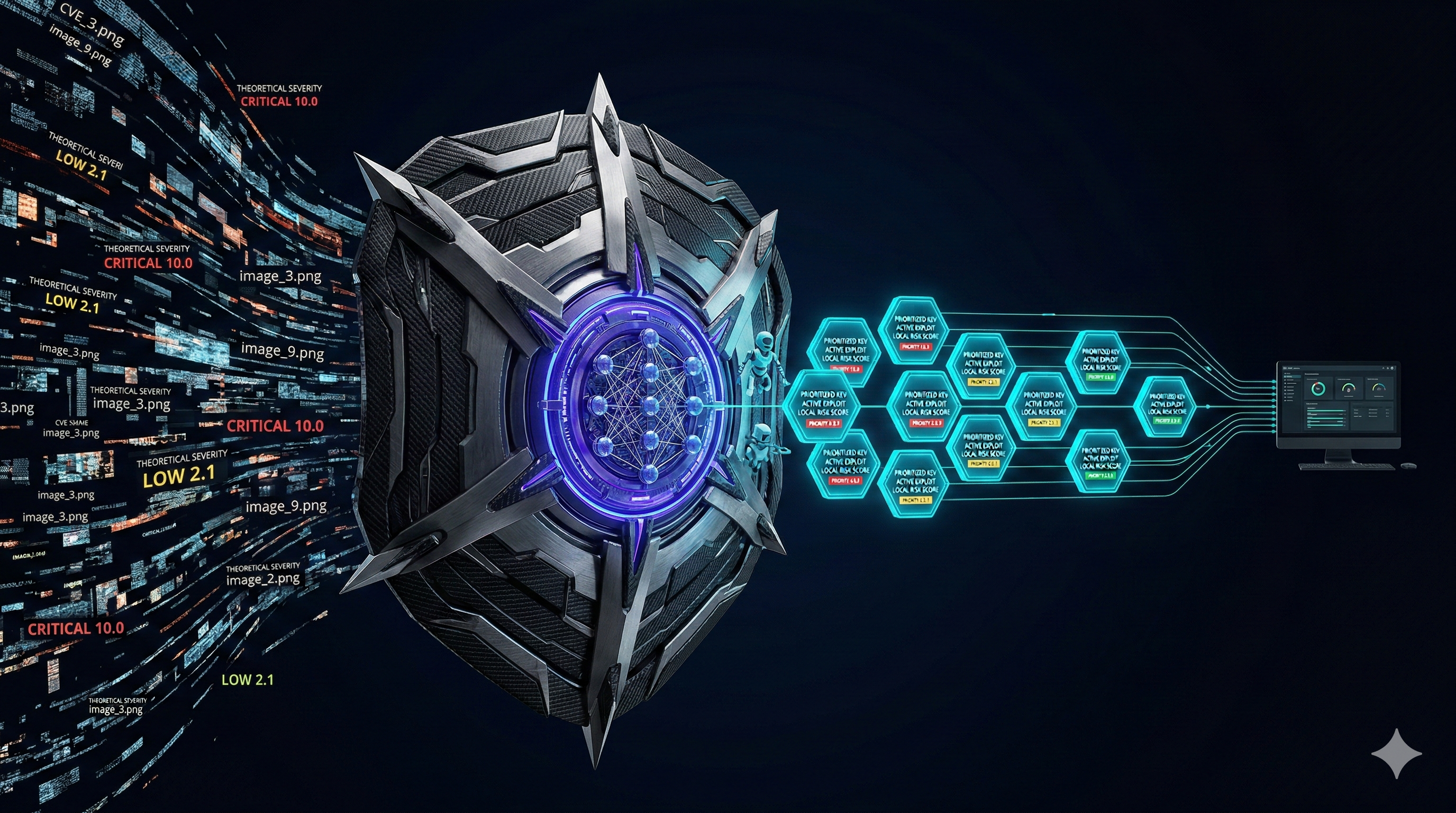
Every security team knows the feeling. You run a scan. Thousands of CVEs pour out, and the majority of them are rated HIGH or CRITICAL by CVSS. Your patch team has capacity to address maybe forty vulnerabilities a quarter. So you work top-down by CVSS score, and somehow, six months later, you still get breached by a vulnerability that was rated 6.5.
This is not bad luck. This is a systematic failure of the tool you were given to prioritize.
What CVSS Actually Measures
The Common Vulnerability Scoring System assigns a number between 0 and 10 based on six factors: attack vector, attack complexity, privileges required, user interaction, scope, and the CIA impact (confidentiality, integrity, availability). These factors are evaluated in a vacuum, the "worst plausible scenario" for a generic installation.
That means CVE-2024-XXXX affecting a component you don't run, on a system you don't expose, in an attack scenario that requires physical access can score 9.8 CRITICAL, and legitimately so, by the CVSS specification. The score isn't wrong. It's just answering the wrong question.
CVSS answers: "How bad could this be in the worst case?"
What you need to know: "Is this actually going to get me breached this quarter?"
The Three Signals CVSS Ignores
1. Active Exploitation Probability (EPSS)
EPSS, the Exploit Prediction Scoring System from FIRST, assigns each CVE a probability score (0-1) representing the likelihood that it will be exploited in the wild within the next 30 days. It's trained on actual exploit telemetry from honeypots, dark web feeds, malware samples, and PoC repositories across the internet.
The data is stark: only ~4% of all published CVEs are ever exploited in the wild. EPSS identifies which 4%. A CVE with CVSS 10.0 and EPSS 0.003 (0.3%) is dramatically less dangerous than a CVE with CVSS 6.5 and EPSS 0.94 (94%).
2. Known Exploitation in the Wild (CISA KEV)
The CISA Known Exploited Vulnerabilities catalog is the closest thing to a confirmed "enemies are using this right now" signal in the public domain. If a CVE appears in the KEV catalog, it means CISA has confirmed it's being exploited in production environments, not theoretical, not lab-demonstrated, but actively used by threat actors.
KEV status is binary and should be treated as a hard override. Any KEV entry should jump to the front of your queue regardless of CVSS score.
3. Your Specific Context
Even with EPSS and KEV, you're still working with population-level statistics. A CVE with EPSS 0.90 in a healthcare organization's EMR system is categorically different from the same CVE in an air-gapped manufacturing OT network. Your industry, your compliance obligations, and your specific asset criticality all change the calculus.
| CVE | CVSS | EPSS | KEV | TRIS™ score |
|---|---|---|---|---|
| CVE-2024-0001 | 9.8 | 0.003 (0.3%) | No | 34 (Medium) |
| CVE-2024-3094 | 6.7 | 0.942 (94%) | YES | 91 (Critical) |
| CVE-2024-0002 | 10.0 | 0.012 (1.2%) | No | 41 (Medium) |
The pattern is stark. The vulnerability that CVSS screams is critical (9.8, 10.0) can be lower actual-risk than a moderately-scored CVE that's already being exploited in ransomware campaigns and sitting in the CISA KEV catalog.
How the CVEasy TRIS™ score Is Different
The CVEasy TRIS™ score is a 0-95 point formula that answers a different question than CVSS. Instead of "how bad could this be in a vacuum?", it asks: "how likely is this to cause material harm to this specific organization, right now?"
The formula has five components:
- Base severity (CVSS): Your starting point. Still matters, just not the whole story.
- Exploit probability (EPSS): Population-level likelihood of real-world exploitation within 30 days.
- Active exploitation (KEV): Binary signal, confirmed wild exploitation adds a hard multiplier.
- Industry exposure: Healthcare, financial services, and critical infrastructure have different threat profiles than retail or SaaS. Compliance obligations (HIPAA, PCI-DSS, FedRAMP) create regulatory risk on top of operational risk.
- Asset criticality: A vulnerability in your crown-jewel patient database is not equivalent to the same vulnerability in a test instance with no production data.
What This Means for Your Patch Program
If you're running CVSS-only prioritization today, you're probably doing one of these things:
- Patching theoretical critical vulnerabilities that nobody exploits, while ignoring medium-rated CVEs that ransomware groups are actively using
- Setting CVSS thresholds (e.g., "patch everything ≥7.0") that generate hundreds of tickets a sprint, burning out your team
- Reporting "87% of criticals patched in SLA" to leadership while the vulnerabilities that actually matter slip through
The shift to correlated intelligence requires rethinking your SLAs, your ticket routing, and your board-level metrics. But the operational payoff is real: smaller, higher-impact patch batches that dramatically reduce your actual breach probability without burning out your team.
Practical First Steps
You don't need to rip and replace your existing toolchain to start. Three immediate changes:
- Add EPSS to your scanner output. FIRST publishes daily EPSS scores via API for free. Pull them into your existing dashboard even as a secondary column.
- Subscribe to the CISA KEV feed. Every CVE that appears there should immediately jump to P1 regardless of your existing scoring. CISA publishes the catalog as a JSON feed updated multiple times per week.
- Segment your asset inventory by criticality. Even a rough 3-tier classification (crown-jewel / business-critical / low-value) lets you apply a meaningful multiplier to exposure calculation.
Once these signals are flowing, the correlation becomes obvious. Your patch backlog doesn't shrink because you patched more, it shrinks because you stopped patching the wrong things.
The Bottom Line
CVSS isn't broken. It does exactly what it was designed to do. The problem is that most organizations are using it to answer a question it was never designed to answer.
Patch prioritization requires correlated intelligence, the fusion of theoretical severity, real-world exploitation probability, active threat actor behavior, and your specific organizational context. CVSS provides one of those four inputs. The other three are where the actual risk lives.
Your patch backlog isn't a resource problem. It's a signal problem. Fix the signal, and the backlog fixes itself.