The 2024 Verizon DBIR found that vulnerability exploitation as an initial access vector grew 180% year-over-year, driven almost entirely by ransomware groups. The playbook is consistent: identify a high-value vulnerability, acquire or develop an exploit, and deploy at scale within days of PoC publication.
Your traditional patch cycle isn't designed for this tempo. A 30-day patch SLA looks reasonable on paper. Against a threat actor who starts exploiting a CVE 48 hours after the PoC drops, it's a guaranteed breach window.
How Ransomware Groups Select Targets
Understanding the attacker's prioritization logic helps you mirror it defensively. Ransomware operators are rational economic actors; they optimize for maximum impact with minimum effort. Their CVE selection criteria:
- High prevalence: Vulnerabilities in widely-deployed software (VPNs, firewalls, Microsoft Exchange, Apache products) offer the largest attack surface per exploit developed.
- Remote, unauthenticated execution: RCE and authentication bypass vulnerabilities that don't require physical access or credentials, CVSS attack vector "Network" + no privileges required.
- Public exploit availability: Once a reliable PoC is public on GitHub or Exploit-DB, the barrier to weaponization drops to near-zero. Time-to-exploit drops from weeks to hours.
- Low patch rate: CVEs where organizations are known to patch slowly, often because patching requires downtime on critical systems.
This selection criteria maps directly onto EPSS. EPSS is trained on actual observed exploitation, which means the CVEs ransomware groups find attractive tend to score highly on EPSS before they become KEV entries.
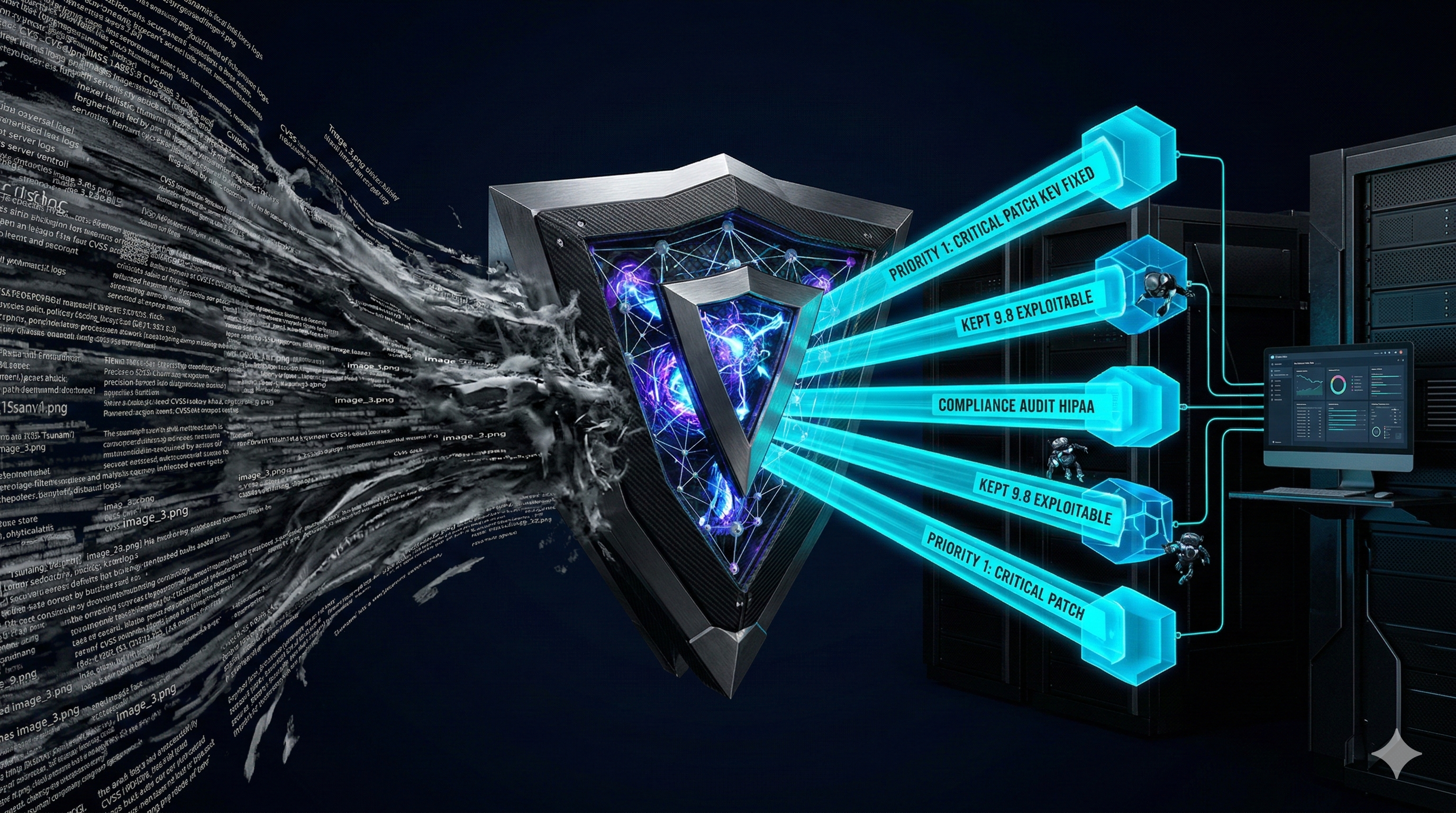
The Predictive Triage Stack
Layer 1: CVSS for Initial Scope
Use CVSS not as your final prioritization metric, but as a filter to reduce scope. Set a threshold, CVSS ≥ 6.0, or RCE/auth bypass specifically, and work within that space. This cuts your universe from 40,000 CVEs to a manageable few thousand without significant risk of missing critical issues.
Layer 2: EPSS for Predictive Exploitation Risk
Within your CVSS-filtered set, sort by EPSS descending. Anything with EPSS ≥ 0.5 (50% exploitation probability within 30 days) should enter an expedited triage lane. Anything ≥ 0.9 is effectively on fire, treat it as an incident response item, not a patch ticket.
Critical nuance: EPSS updates daily. A CVE that was EPSS 0.02 last week can jump to 0.85 overnight when a PoC drops. Monitoring EPSS delta, not just current value, gives you early warning before the KEV catalog confirms exploitation.
Layer 3: KEV as a Hard Override
Any CVE in the CISA KEV catalog is being actively exploited in the wild, confirmed. It doesn't matter where it ranks on CVSS or EPSS. KEV entries bypass your normal prioritization entirely and enter emergency response. Your target: triage within 4 hours, remediation plan within 24 hours, patch or compensating control within 72 hours.
Layer 4: Industry Context
Not all organizations are equally targeted. Ransomware groups specialize. LockBit and Cl0p have demonstrated consistent focus on healthcare and financial services. Volt Typhoon targets critical infrastructure. Your industry shapes which CVEs are most likely to be weaponized against your specific environment.
| Signal | Target Triage | Target Patch/Mitigate |
|---|---|---|
| KEV entry | < 4 hours | 72 hours |
| EPSS ≥ 0.9 | < 24 hours | 7 days |
| EPSS 0.5-0.9 | < 48 hours | 14 days |
| CVSS ≥ 7.0, EPSS < 0.5 | Standard triage | 30 days |
The Pre-Exploitation Window: Your Actual Opportunity
The insight that transforms ransomware defense: there's a predictable window between CVE publication and active exploitation. EPSS identifies CVEs that are trending toward weaponization before the weapon is built.
A CVE that jumps from EPSS 0.01 to 0.40 in a week is a warning signal: the security research community is paying attention to it, PoC development is likely underway, and KEV listing may be days away. Patching during this window, before exploitation is confirmed, eliminates your exposure entirely.
This is why monitoring EPSS delta is more valuable than monitoring EPSS absolute value. You want to catch the rising curve, not confirm the explosion after it happens.
Compensating Controls When You Can't Patch
Not every critical vulnerability can be patched on an emergency timeline. VPN appliances, OT systems, legacy applications, and systems requiring maintenance windows create patch gaps. For these, compensating controls buy time:
- Network segmentation: Isolate vulnerable systems from pathways an attacker would use to move laterally post-exploitation.
- Temporary disable: If the vulnerable component is non-essential (an API endpoint, a protocol, a service), disable it until patching is possible.
- WAF / IPS signatures: Many ransomware groups use known exploit signatures. Deploy IPS signatures specific to the CVE as a short-term measure.
- Enhanced monitoring: If you can't block the attack, make sure you'll detect it. Deploy specific detection rules for exploitation attempts.
Building the Ransomware-Specific Queue
Operationally, implement a dedicated ransomware triage lane alongside your standard vulnerability queue:
- Filter your CVE inventory daily to: KEV = YES OR EPSS ≥ 0.5
- Apply industry-specific filters (healthcare: focus on VPN, RDP, remote access; finance: focus on web-facing applications and payment systems)
- Cross-reference against your asset inventory, a KEV CVE that doesn't affect any of your systems still needs to be confirmed and documented as not applicable
- Auto-escalate anything that moves: if EPSS jumps ≥ 0.3 in 7 days, pull it into the expedited lane regardless of absolute value
- Track resolution velocity separately, your ransomware response speed is a distinct capability from general patch management
Ransomware groups exploit speed asymmetry. They move faster than traditional patch programs. Correlated intelligence, EPSS + KEV + industry context, is how you move fast enough to defend against them.