CVSS vs EPSS vs TRIS: Which Vulnerability Scoring System Should You Trust?
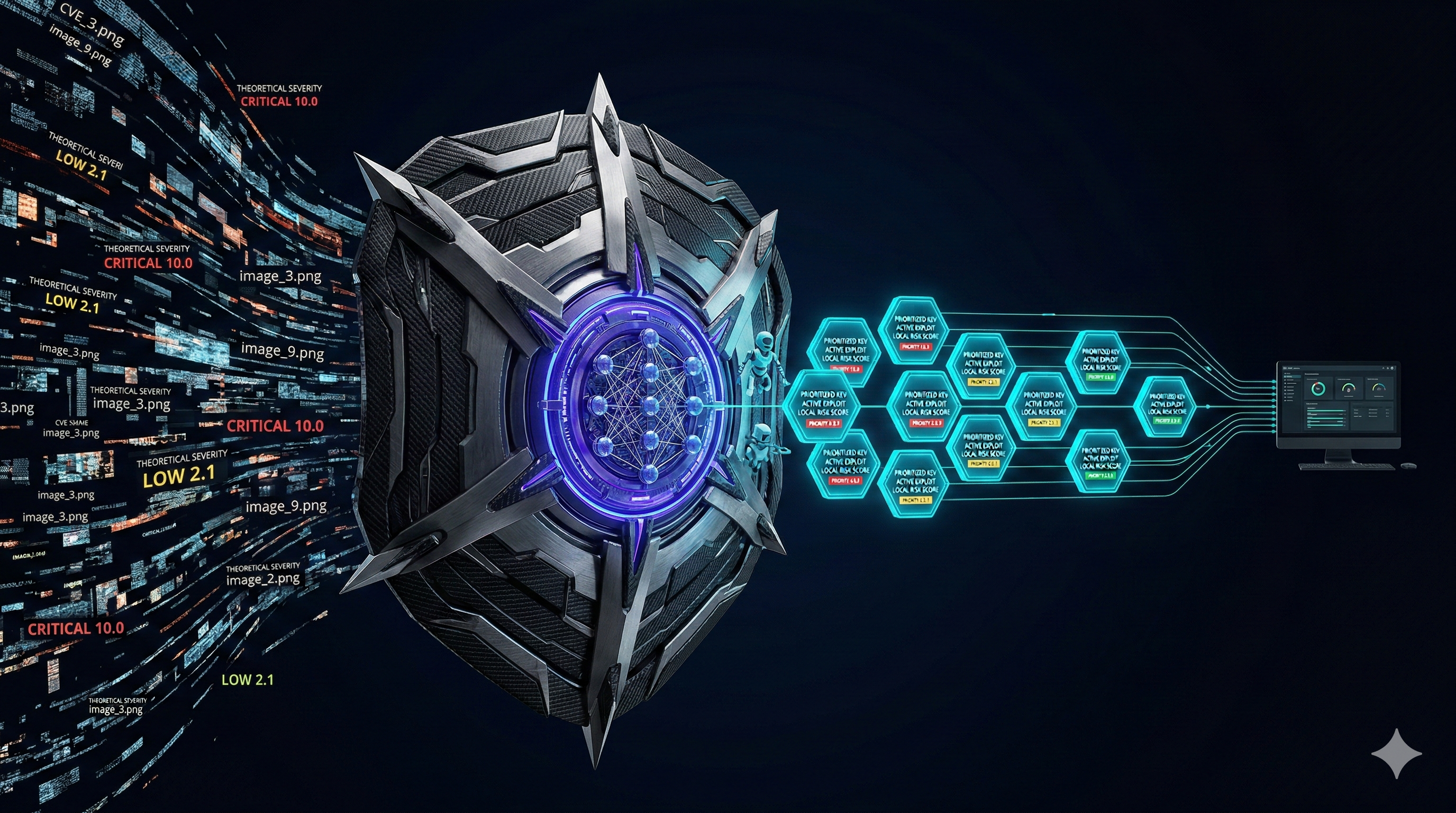
Every security team faces the same fundamental problem: you have thousands of vulnerabilities and limited resources. The scoring system you use to prioritize determines which vulnerabilities get fixed and which sit in the backlog. Choose the wrong system and you spend months patching theoretical risks while actively exploited vulnerabilities go unaddressed.
Three scoring systems dominate the conversation in 2026: CVSS (Common Vulnerability Scoring System), EPSS (Exploit Prediction Scoring System), and TRIS (TrueRisk Intelligence Score). Each takes a fundamentally different approach to the same question: what should we fix first?
This post breaks down how each system works, where each fails, and why the future of vulnerability prioritization requires more than a single number.
CVSS: The Foundation That Became a Crutch
How CVSS Works
CVSS was developed by NIST and is maintained by FIRST.org. It measures the technical severity of a vulnerability using a standardized set of metrics. The current version, CVSS v4.0, evaluates a vulnerability across four metric groups:
- Base Metrics: Attack vector, attack complexity, privileges required, user interaction, scope, and impact on confidentiality, integrity, and availability
- Threat Metrics: Exploit code maturity (new in v4.0, replacing Temporal)
- Environmental Metrics: Modified base metrics adjusted for your specific environment (rarely used in practice)
- Supplemental Metrics: Safety, automatable, recovery, value density, provider urgency (new in v4.0)
The output is a score from 0.0 to 10.0 with severity labels: None (0.0), Low (0.1-3.9), Medium (4.0-6.9), High (7.0-8.9), and Critical (9.0-10.0).
Where CVSS Fails
CVSS was designed to answer one question: "How technically severe is this vulnerability?" It was never designed to answer the question security teams actually need answered: "How urgently should I fix this vulnerability in my environment?" These are fundamentally different questions, and using CVSS to answer the second one creates serious problems.
Here are the specific failure modes:
- CVSS scores are static. A score assigned when a CVE is published never changes, even as the threat landscape evolves. A CVSS 9.8 from 2019 with no exploit still reads as 9.8 in 2026. The real-world risk has changed dramatically, but the score has not.
- CVSS ignores exploit availability. The base score does not consider whether anyone has written an exploit, whether it is being used in the wild, or whether threat actors are targeting it. A theoretically severe vulnerability with no public exploit gets the same urgency as one being actively used by ransomware groups.
- CVSS has no context. A CVSS 9.8 on a development laptop that never leaves your office and a CVSS 9.8 on a public-facing production database get the same score. The risk is not remotely the same.
- CVSS creates alert fatigue. When everything is Critical, nothing is. The average enterprise has thousands of Critical and High CVSS findings. Teams cannot patch all of them, so they either try to patch everything (and burn out) or start ignoring the scores entirely.
For a deeper analysis of CVSS limitations, read our post on why CVSS alone is creating your patch backlog.
EPSS: Predicting What Actually Gets Exploited
How EPSS Works
EPSS was developed by FIRST.org (the same organization that maintains CVSS) as a direct response to the limitations of severity-only scoring. Instead of asking "how severe is this vulnerability?", EPSS asks "what is the probability that this vulnerability will be exploited in the wild within the next 30 days?"
EPSS uses a machine learning model trained on observed exploitation data from multiple sources including IDS/IPS signatures, exploit databases, honeypots, and threat intelligence feeds. The model considers over 1,400 features for each CVE, including:
- Days since publication
- Vendor and product category
- Whether exploit code exists on Exploit-DB, Metasploit, or GitHub
- References to the CVE on dark web forums and paste sites
- Social media mentions and security researcher activity
- CVSS vector components (as features, not as the score itself)
- Historical exploitation patterns for similar vulnerability types
The output is a probability between 0 and 1. An EPSS score of 0.85 means there is an 85% chance this CVE will be exploited in the next 30 days. An EPSS score of 0.003 means a 0.3% chance.
What EPSS Gets Right
EPSS represents a massive improvement over CVSS for prioritization. Research from FIRST.org shows that using EPSS to prioritize the top 10% of vulnerabilities by exploitation probability captures over 60% of all actually exploited CVEs while only requiring you to address 10% of your total findings. CVSS prioritization of the top 10% by severity score captures less than 30% of exploited CVEs.
Put simply: EPSS is significantly better at identifying what attackers will actually target.
Where EPSS Falls Short
EPSS is a prediction model, and like all prediction models, it has limitations:
- EPSS has no environmental context. An EPSS score of 0.9 means the CVE is likely to be exploited somewhere in the world. It says nothing about whether it is exploitable in your specific environment, on your specific asset, with your specific compensating controls.
- EPSS does not know your assets. A high-EPSS vulnerability on an air-gapped test server is very different from the same vulnerability on a public-facing production database. EPSS cannot distinguish between these because it has no visibility into your infrastructure.
- EPSS is probabilistic, not validated. It predicts exploitation probability based on historical patterns. It does not prove whether a vulnerability is actually exploitable right now in your configuration. Prediction and validation are different things.
- EPSS can lag zero-days. The model is trained on historical data. A brand new zero-day with no exploitation history may receive a low initial EPSS score even when it is being actively exploited, simply because the model has not yet observed exploitation signals.
- EPSS does not track threat actors. It predicts exploitation probability in aggregate. It does not tell you whether APT29, FIN7, or a specific ransomware group is targeting a CVE. Industry-specific threat context is absent.
For a deeper look at how EPSS fits into a broader scoring strategy, see our post on EPSS + KEV + enterprise context.
TRIS: Seven Layers of Intelligence
How TRIS Works
TRIS (TrueRisk Intelligence Score) is the proprietary scoring system built into CVEasy AI. It was designed from the ground up to solve the problems that both CVSS and EPSS leave unaddressed. Rather than relying on a single signal, TRIS combines seven independent intelligence layers into a weighted composite score from 0 to 100.
Here is the formula:
TRIS = w1(CVSS) + w2(EPSS) + w3(KEV) + w4(ThreatActor) + w5(AssetCrit) + w6(Exposure) + w7(BASzy)The Seven Layers
Layer 1: CVSS Base Score (Weight: 15%)
TRIS does not discard CVSS. Technical severity still matters. But TRIS reduces its weight to 15% of the total score, reflecting the reality that severity alone is a poor predictor of real-world risk. A CVSS 9.8 and a CVSS 7.5 may receive similar TRIS scores depending on the other six layers.
Layer 2: EPSS Weaponization Probability (Weight: 20%)
EPSS is one of the strongest predictive signals available. TRIS weights it at 20% because real-world exploitation probability is more actionable than theoretical severity. A CVE with an EPSS score above 0.5 (50% chance of exploitation in 30 days) receives a major TRIS boost regardless of its CVSS score.
Layer 3: CISA KEV Active Exploitation (Weight: 20%)
The CISA Known Exploited Vulnerabilities catalog is the definitive list of CVEs currently being used in real attacks. This layer is binary: if a CVE is on the KEV list, it receives maximum weight. If it is not, this layer contributes zero. CISA mandates that federal agencies patch KEV entries within 14 days, and for good reason. Our deep dive on the CISA KEV catalog covers why this matters.
Layer 4: Threat Actor Targeting (Weight: 15%)
TRIS tracks 49 APT groups and their known toolkits, TTPs, and targeted industries. If APT29 (Cozy Bear) is known to exploit a specific CVE and your organization operates in their target industry (government, defense, energy), this layer significantly boosts the TRIS score. This is the threat context that neither CVSS nor EPSS provide.
Layer 5: Asset Criticality (Weight: 10%)
Not all assets are equal. A vulnerability on a development laptop is less urgent than the same vulnerability on a production domain controller. TRIS automatically classifies assets by role (web server, database, domain controller, workstation) and business criticality. Crown jewel assets receive maximum weight.
Layer 6: Public Exposure (Weight: 10%)
Internet-facing assets with exploitable vulnerabilities are exponentially more urgent than internal-only assets with the same CVE. TRIS factors in whether the affected asset is publicly accessible, on which ports, and whether those ports are running the vulnerable service. This layer matters because attack surface management begins with understanding exposure.
Layer 7: BASzy Exploit Validation (Weight: 10%)
This is what makes TRIS unique. BASzy runs real attack simulations against your environment and proves whether a vulnerability is actually exploitable in your specific configuration. A CVE that is theoretically critical but blocked by your WAF, EDR, or network segmentation receives a TRIS reduction. A CVE that BASzy proves is exploitable with no detection receives a major boost. This is the "validate" stage of CTEM that no other scoring system includes. Read our guide to breach and attack simulation for more on why validation changes the game.
The Same CVE, Scored Three Ways
Theory is useful, but a concrete example makes the differences clear. Let us take a real-world scenario with two vulnerabilities and see how CVSS, EPSS, and TRIS each prioritize them.
CVE-2024-21762: Fortinet FortiOS Out-of-Bound Write
| Signal | CVE-2024-21762 (FortiOS) | CVE-2024-3400 (PAN-OS) |
|---|---|---|
| CVSS Score | 9.8 (Critical) | 10.0 (Critical) |
| EPSS Score | 0.93 (93%) | 0.97 (97%) |
| CISA KEV | Yes | Yes |
| Threat Actors | APT28 (Fancy Bear), multiple ransomware groups | UTA0218 (state-sponsored), ransomware groups |
| Your Asset | Internal-only FortiGate (management VLAN, no public exposure) | Internet-facing PA-5200 (primary perimeter firewall) |
| Exposure | Not publicly reachable | Public IP on ports 443, 80 |
| BASzy Result | Exploit blocked by network segmentation | Exploitable, full command execution confirmed |
How Each System Prioritizes
| Scoring System | CVE-2024-21762 Priority | CVE-2024-3400 Priority | Fix First |
|---|---|---|---|
| CVSS | 9.8. Critical | 10.0. Critical | CVE-2024-3400 (by 0.2 points) |
| EPSS | 0.93. Very High | 0.97. Very High | CVE-2024-3400 (by 0.04 points) |
| TRIS | TRIS 52. Medium | TRIS 97. Critical | CVE-2024-3400 (by 45 points) |
All three systems agree that CVE-2024-3400 should be fixed first. But the degree of differentiation tells a completely different story.
CVSS sees both as essentially equal. They are 0.2 points apart. A security team using CVSS would treat them with identical urgency, potentially patching whichever is more convenient first.
EPSS sees both as very high probability exploitation targets. The difference is 0.04 points. Again, a team using EPSS alone would reasonably treat them as equal priority.
TRIS sees a 45-point gap. CVE-2024-3400 scores 97 because it hits on all seven layers: high severity, near-certain exploitation, on the KEV list, targeted by state-sponsored actors, on a critical perimeter asset, publicly exposed, and validated as exploitable by BASzy. CVE-2024-21762 scores 52 because, despite its high CVSS and EPSS scores and KEV presence, it is on an internal-only asset that is not publicly exposed and BASzy proved the exploit is blocked by network segmentation. The risk is real but the urgency is dramatically lower.
A Side-by-Side Comparison
| Capability | CVSS | EPSS | TRIS |
|---|---|---|---|
| Measures technical severity | Yes (primary purpose) | No | Yes (Layer 1, 15%) |
| Predicts exploitation probability | No | Yes (primary purpose) | Yes (Layer 2, 20%) |
| Tracks active exploitation | No | Indirectly | Yes (Layer 3, KEV, 20%) |
| Threat actor context | No | No | Yes (Layer 4, 49 APTs, 15%) |
| Asset criticality awareness | No (env, metrics rarely used) | No | Yes (Layer 5, auto-classified, 10%) |
| Public exposure awareness | Attack vector only | No | Yes (Layer 6, auto-detected, 10%) |
| Exploit validation | No | No | Yes (Layer 7, BASzy, 10%) |
| Scores update dynamically | Never | Daily | Real-time |
| Maintained by | FIRST.org / NVD | FIRST.org | CVEasy AI |
| Open standard | Yes | Yes | Proprietary |
| Scale | 0.0, 10.0 | 0, 1 (probability) | 0 - 100 |
Common Objections and Honest Answers
"CVSS is good enough for compliance"
This is technically true. Most compliance frameworks (PCI DSS, HIPAA, SOC 2, FedRAMP) reference CVSS scores as thresholds for patch SLAs. You need CVSS for compliance. But compliance is the floor, not the ceiling. Meeting a "patch all Criticals in 30 days" SLA does not mean you are secure. It means you are compliant. Those are different things. TRIS gives you CVSS-based compliance reporting and risk-based operational prioritization in the same platform.
"EPSS is enough if we combine it with CVSS"
Combining CVSS and EPSS is better than either alone. Several vendors do this. But two signals still miss three critical dimensions: your asset context, your exposure profile, and whether the vulnerability is actually exploitable in your specific environment. A CVE with a CVSS 9.8 and EPSS 0.95 that is blocked by your WAF is less urgent than a CVE with CVSS 7.5 and EPSS 0.6 that BASzy proves is exploitable on your unprotected production database. Two signals cannot make this distinction. Seven can.
"TRIS is proprietary, so we cannot audit it"
Fair concern. The TRIS methodology white paper documents all seven layers, their weights, and the data sources for each. Every TRIS score in CVEasy AI shows the contribution from each layer, so you can see exactly why a vulnerability received its score. Transparency is a design principle, not an afterthought. We also want to point out that Tenable VPR, Qualys TruRisk, and CrowdStrike ExPRT.AI are all proprietary scoring systems that provide less transparency about their methodology than TRIS does.
"We should just focus on KEV and patch those first"
KEV-first is a strong strategy and vastly better than CVSS-first. But the KEV catalog is intentionally conservative. CISA only adds CVEs with confirmed active exploitation AND a clear remediation path. There are actively exploited vulnerabilities that are not yet on KEV. TRIS uses KEV as one of seven signals, not the only signal. This catches both the confirmed-exploited (KEV) and the likely-to-be-exploited-next (EPSS + threat actor targeting).
When to Use Each System
These systems are not mutually exclusive. Here is a practical guide for when each one adds the most value:
Use CVSS when you need a standardized severity assessment for compliance reporting, vendor advisories, or communicating with non-technical stakeholders who understand the 0-10 scale. CVSS is a universal language.
Use EPSS when you want to filter noise quickly. If you have 10,000 open findings and need to cut to the ones most likely to be exploited soon, sorting by EPSS is a fast way to separate signal from noise. EPSS is freely available at api.first.org and does not require any commercial tool.
Use TRIS when you need to make real-world patching decisions that account for your specific environment, assets, exposure, and validated exploitability. TRIS is the operational scoring system that drives daily prioritization. It is built into CVEasy AI and runs automatically on every imported scan.
Building a Scoring Strategy
If you are designing a vulnerability management program from scratch, here is how to build a scoring strategy that works:
- Start with EPSS to filter. Any CVE with EPSS below 0.1 (10% exploitation probability) can be deprioritized in most environments. This immediately reduces your actionable finding count by 80-90%.
- Use KEV as a hard override. Anything on the CISA KEV list gets patched regardless of other scores. No exceptions, no delays.
- Layer in asset context. A High-EPSS finding on a development VM is less urgent than a Medium-EPSS finding on a production database. Your scoring system needs to know which assets matter.
- Validate with BAS. Before dedicating engineering time to a complex patch, prove the vulnerability is actually exploitable in your environment. BASzy does this automatically for 12,868 attack techniques mapped to MITRE ATT&CK.
- Report with CVSS. When presenting to the board or meeting compliance requirements, translate your TRIS-driven priorities back into CVSS language that auditors understand. See our CISO board reporting guide for practical templates.
For a full guide to building this workflow, read building a vulnerability management program from scratch.
The Future of Vulnerability Scoring
The industry is moving away from single-signal scoring. CVSS will remain the universal severity language, the same way Fahrenheit and Celsius remain temperature scales even though neither tells you whether to bring an umbrella. EPSS will become table stakes for any serious vulnerability management platform. The competitive frontier is in environmental context, threat intelligence correlation, and exploit validation.
Gartner's CTEM framework explicitly includes "validation" as a required stage. Scoring systems that cannot incorporate validation data will increasingly fall behind. TRIS is built around this insight: the score should change when you prove whether a vulnerability is actually exploitable, not just when someone publishes a new advisory.