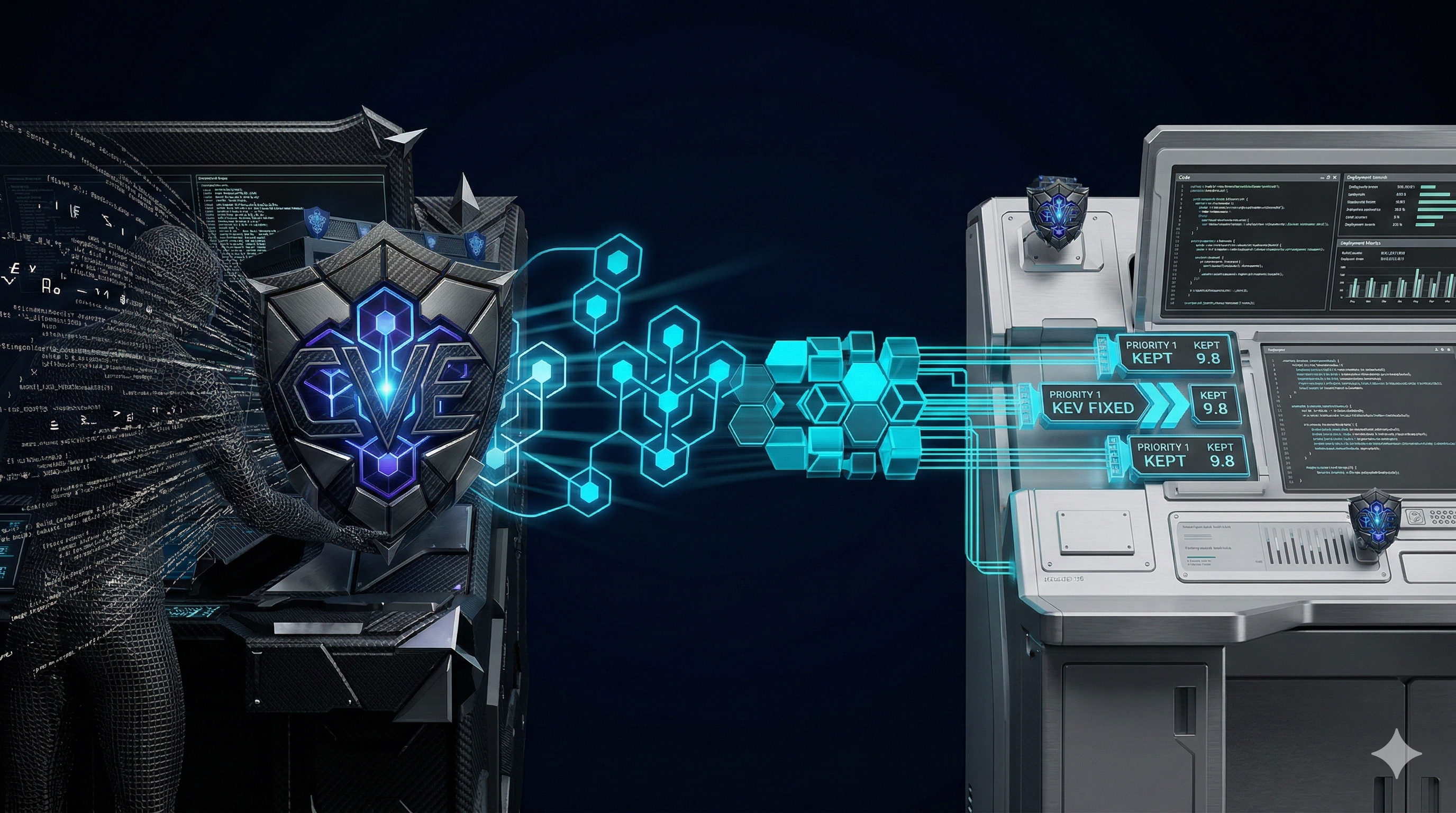
Vulnerability scoring has evolved significantly since CVSS was introduced in 2005. Two major additions, EPSS (2019) and the CISA KEV catalog (2021), have given security teams the raw materials to build a genuinely predictive prioritization model. The challenge is knowing how to weight and combine them.
This article breaks down each layer of the scoring stack, explains the data sources and update cadences, and walks through the CVEasy TRIS™ score formula that combines all three.
Layer 1: CVSS, The Severity Foundation
CVSS (Common Vulnerability Scoring System) v3.1 scores vulnerabilities on a 0-10 scale based on six base metrics:
- Attack Vector (AV): Network, Adjacent, Local, or Physical
- Attack Complexity (AC): Low or High
- Privileges Required (PR): None, Low, or High
- User Interaction (UI): None or Required
- Scope (S): Unchanged or Changed
- CIA Impact (C/I/A): None, Low, or High for each
CVSS is published by NVD within days of CVE creation and is available for all ~240,000 CVEs in the NVD database. It's the most comprehensive and consistent scoring signal available, which is why it remains a useful foundation, not as a final answer, but as a starting filter.
Use CVSS to set scope. Use EPSS and KEV to set order. Use enterprise context to set urgency.
Layer 2: EPSS, The Exploitation Probability Signal
EPSS (Exploit Prediction Scoring System) is maintained by FIRST and published daily. Each CVE receives a score between 0 and 1 representing the probability of exploitation in the wild within the next 30 days.
How EPSS Is Calculated
EPSS v3 (released 2023) is a machine learning model trained on data from multiple sources:
- Exploit-DB, GitHub, NVD reference links (PoC availability signals)
- Threat intelligence feeds (honeypot telemetry, darkweb forums)
- Malware sample analysis (CVEs embedded in malware samples)
- Historical exploitation data (what was exploited before, under what conditions)
The model outputs a probability and a percentile. The percentile is often more useful than the raw probability, a CVE at the 95th percentile is more concerning than one at the 70th, regardless of whether the absolute probability is 0.4 or 0.9.
EPSS Update Cadence and Delta Tracking
EPSS updates daily. A CVE that was at EPSS 0.01 last Monday can jump to 0.6 this Monday if a working PoC is published over the weekend. Tracking EPSS delta, the rate of change over time, is more valuable than tracking the current score in isolation.
A 7-day EPSS delta ≥ 0.2 is a strong signal that exploitation development is underway. In practice, this pattern precedes KEV listing by 3-14 days in the majority of cases.
Layer 3: KEV, The Confirmed Exploitation Signal
The CISA Known Exploited Vulnerabilities (KEV) catalog is the most unambiguous signal available: these CVEs are being actively exploited in the wild, confirmed by CISA. New entries are added multiple times per week.
KEV should be treated as a binary override signal, not a scoring component. Any KEV entry immediately jumps to your highest priority tier regardless of CVSS or EPSS score. The question is no longer "is this risky?", CISA has answered that. The question is "how fast can we mitigate it?"
Layer 4: Enterprise Context, The Organization-Specific Multiplier
The first three layers are population-level signals. They tell you what's dangerous to organizations in general. The fourth layer converts that to risk for your organization specifically.
Industry Exposure Multipliers
Different industries face different threat actors with different toolkits. CVEasy AI applies industry-specific multipliers calibrated to known threat actor targeting patterns:
Compliance Obligation Weighting
Compliance frameworks create legal and regulatory risk on top of operational risk. A vulnerability that could cause a HIPAA breach or PCI-DSS fine carries additional organizational cost beyond the direct security impact. Compliance flags add a risk premium to affected CVEs.
Asset Criticality
A vulnerability affecting your patient records database is categorically different from the same CVE in a dev environment. Even a rough three-tier asset classification (crown jewel / business critical / low value) applies a meaningful multiplier.
The CVEasy TRIS™ score Formula
Score Band Interpretation
| Score Range | Band | Action |
|---|---|---|
| 75-95 | CRITICAL | Immediate response, 72-hour SLA |
| 50-74 | HIGH | Expedited triage, 14-day SLA |
| 25-49 | MEDIUM | Standard triage, 30-day SLA |
| 0-24 | LOW | Next patch cycle or dismiss |
The scoring stack isn't magic. It's systematic application of publicly available threat intelligence, calibrated to your specific organizational risk profile. The organizations that implement this model consistently report the same outcome: fewer vulnerabilities to chase, faster response on the ones that matter, and a dramatic reduction in breach risk from exploitable CVEs.